CISSP PRACTICE QUESTIONS – 20210401 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu

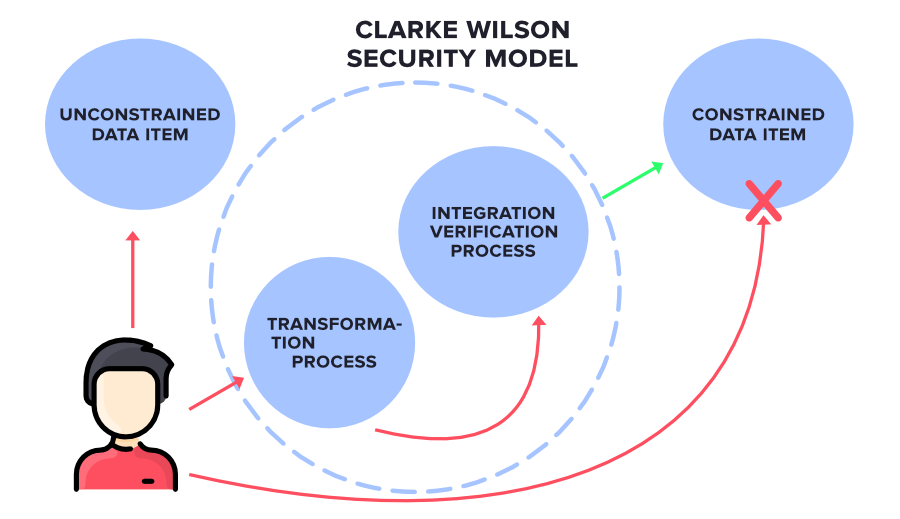
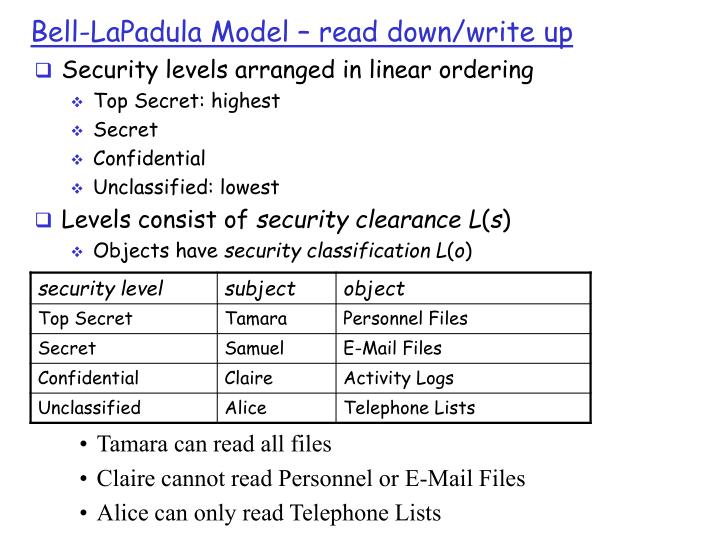
This model focuses on integrity at the transaction level and addresses three major goals of integrity in a commercial environment. - Skillset